The holiday shopping season is approaching, and many consumers will find their gifts online. After all, cyber Monday has practically turned into its own major holiday. Unfortunately, as online shopping continues to grow, so does the targeting of consumers through malicious look-alike domains.
Cyber attackers create fraudulent domains by substituting a few characters in the URLs. Because they point to malicious online shopping websites that closely mimic legitimate, well-known retail websites, it makes it increasingly difficult for customers to detect fake domains. Additionally, given that many of these malicious pages use a trusted TLS certificate, they appear to be safe to online shoppers who unknowingly provide sensitive account information and payment data.
But just how prominent are these look-alike domains?
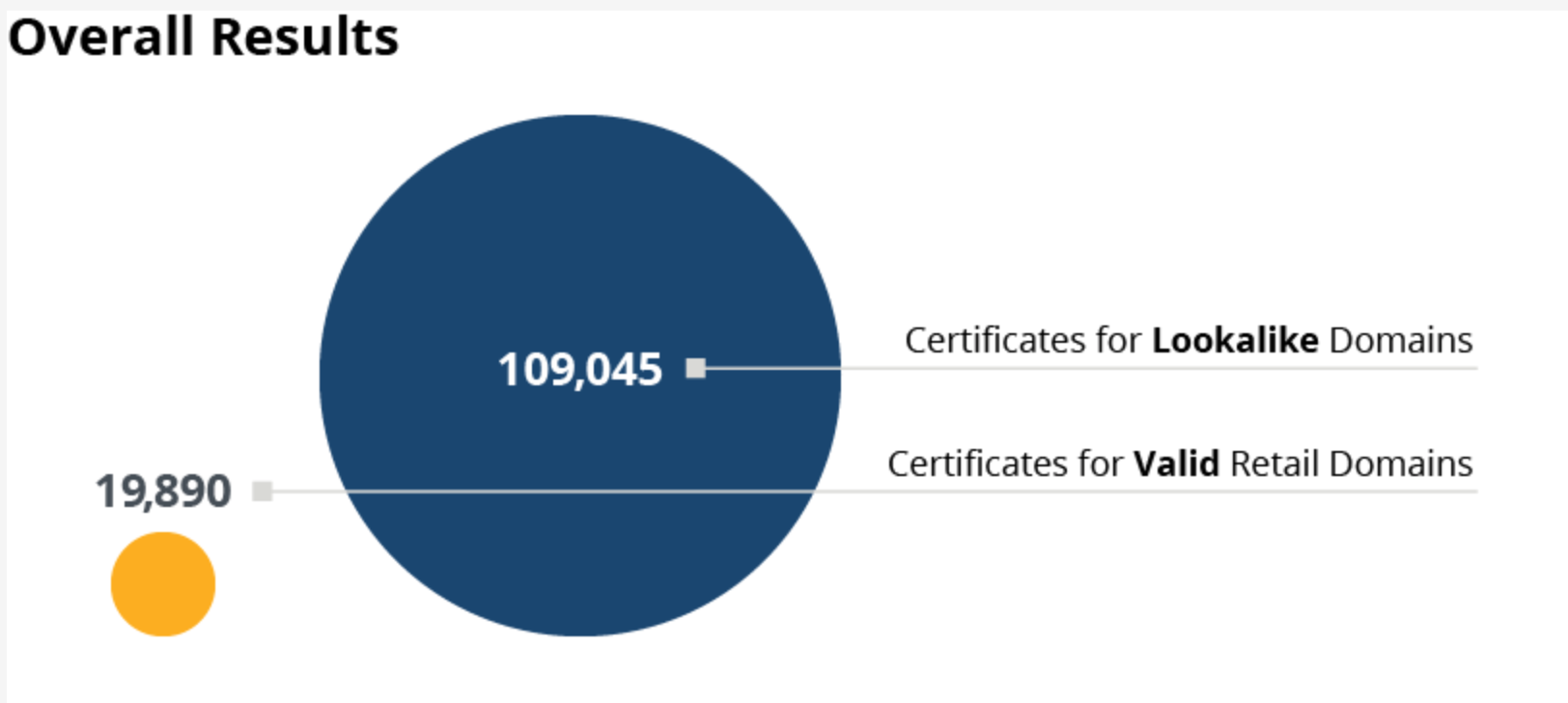
Venafi recently conducted research on the explosion of lookalike domains, which are often used to steal sensitive data from online shoppers. We analyzed suspicious domains targeting 20 major retailers in the U.S., U.K., France, Germany and Australia and found over 100,000 lookalike domains that use valid TLS certificates to appear safe and trusted.
Major overall findings from the research include the following:
- Growth in the number of look-alike domains has more than doubled since 2018, outpacing legitimate domains by nearly four times.
- The total number of certificates used for look-alike domains is more than 400% greater than the number of authentic retail domains.
- Over half (60%) of the look-alike domains studied use free certificates from Let’s Encrypt.
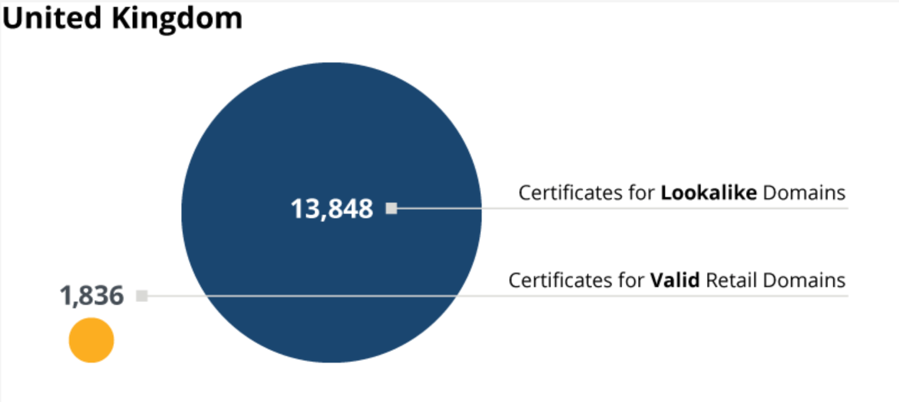
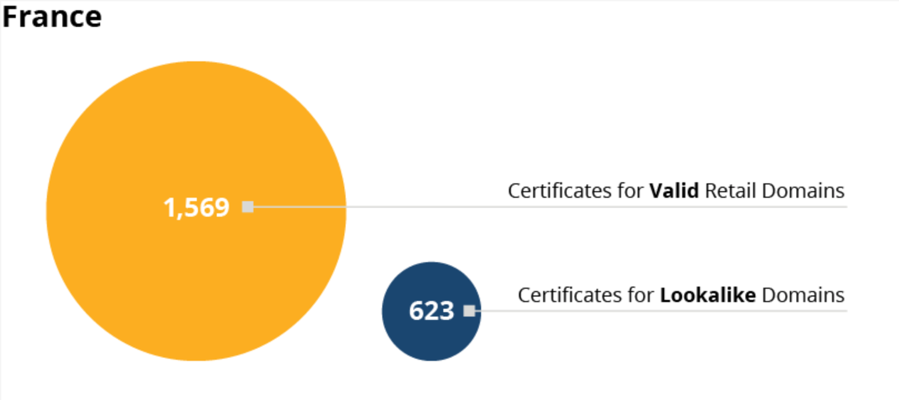
Every region had its own challenges with lookalike domains. Below you can find interesting statistics and breakdowns from each country.
One of the top U.S. retailers has over 49,500 look-alike domains targeting their customers.

The United Kingdom has the largest ratio of look-alike domains targeting retailers, with are over six times more look-alike domains than valid domains.
The look-alike domains in Germany are more likely to use certificates from Let’s Encrypt than any other region. 85% of look-alike domains use Let’s Encrypt.

One of the top retailers in Australia had over 2,000 look-alike domains targeting their customers. This contributed to over half of the look-alike domains in the region.

France is the only country with a relatively low ratio of lookalike domains relative to legitimate domains
What can retailers do to protect themselves?
As the holiday shopping season approaches, the number of look-alike domains targeting online shoppers will multiply. Online retailers that discover malicious domains can take several steps to protect their customers, including:
- Search and report suspicious domains using Google Safe Browsing. Google Safe Browsing is an industry anti-phishing service that identifies and blacklists dangerous websites. Retailers can report a suspicious domain at https://safebrowsing.google.com/safebrowsing/report_general
- Add Certificate Authority Authorization (CAA) to the DNS records of domains and subdomains. CAA lets organizations determine which CAs can issue certificates for domains they own. It is an extension of the domain’s DNS record and supports property tags that let owners set CA policy for entire domains or for specific hostnames.
- Leverage technology solutions to search for suspicious domains. Brand protection services may help retailers find malicious websites and stop the unauthorized use of their logos or brands. Solutions that also provide anti-phishing functionality can help aid in the search for look-alike domains.
- Detect malicious certificates using Certificate Transparency. All publicly trusted machine identities, such as TLS certificates, are published to open logs. Monitoring and analyzing these logs enable organizations to detect look-alike domains and certificates before they are used in attacks against customers.
"Rampant Growth" in Look-Alike Domains
“We continue to see rampant growth in the number of malicious, look-alike domains used in predatory phishing attacks,” said Jing Xie, senior threat intelligence researcher at Venafi. “This is a result of the push to encrypt more and potentially all web traffic, a trend that generally improves security for users but inadvertently introduces a new challenge to existing methods of phishing detection. Most businesses and many retailers don’t have the updated technology in place to find these malicious sites and remove them to protect their customers.”
Are you looking out for look-alike domains?

SSL/TLS Certificates and Their Prevalence on the Dark Web
Related posts
- Domain Spoofing Is Still a Serious Threat for Online Retailers
- The London Protocol Aims to Expose the Misuse of Machine Identities in Phishing Attacks
- Phishing Campaign Uses TLS Certificates to Impersonate Netflix and Steal Users’ Account Credentials
- PayPal Phishing Fiascos: Protecting Yourself from Fraudulent Certificates
