In my previous post (What Is Public Key Encryption), I provide an overview of encryption and why organizations need to use it to manage and protect machine communications and data. In this post, I look at the two types of encryption keys that are used in machine identity management, the public key and the private key—and how the two types differ.
Public key encryption plays a pivotal role in ensuring secure communication and data protection. Within this system, two distinct types of keys operate - the public key and the private key. Both keys, despite being part of the same pair, have different roles. The public key, as the name suggests, is openly accessible and used to encrypt data. Conversely, the private key is kept confidential and used to decrypt the data. Any information encoded using the public key can only be decoded with its corresponding private key. This two-key system forms the backbone of secure machine identity management, effectively safeguarding the integrity of machine communications.

TLS Machine Identity Management for Dummies
What is a public key?
A public key is used in asymmetric encryption and is paired with a private key. The public key is associated with an owner and may be made public. Like a web address, anyone can look it up and share it widely. Once the sender has the public key, they use it to encrypt their message.
In the case of digital signatures, the public key is used to verify a digital signature that was generated using the corresponding private key. When a client wishes to establish a secure connection with a server, it first checks the server’s digital certificate. Then, the client generates a session key that it encrypts with the server’s public key.
What is a private key?
A private key, also known as a secret key, is used to encrypt and decrypt data. Only the key's generator or those authorized to decrypt the data should know the secret key. Private keys are crucial in symmetric and asymmetric cryptography.
The private key can only be accessed by the owner of a digital certificate, and they can choose where the public key goes. A certificate is essentially a way of handing out that public key to users that the owner wants to have it.
Typically, a private key is a lengthy, randomly or pseudo-randomly generated sequence of bits that is difficult to deduce. The complexity and length of the private key determine the strength of the encryption algorithm and influence how easily a brute-force attack may be launched.
Public key vs private key: An overview
Private and public PKI keys must work together. A file that is encrypted by the private key can only be decrypted by the public key, and vice versa. If the public key can only decrypt the file that has been encrypted by the private key, being able to decrypt that file assures that the intended receiver and sender took part in the informational transaction. But there are still cases where private key cryptography is more appropriate.
Indeed, there are some significant differences between public key and private key cryptography, as shown in the following chart.
Difference between private key and public key cryptography
| Private Key Cryptography | Public Key Cryptography |
| The same key is used to encrypt and decrypt a message | Two keys are used, one for encryption and the other for decryption |
| Supports asymmetrical encryption which uses only one secret key | Supports symmetrical encryption which uses two types of keys: private and public keys |
| Sender and receiver share the same key | Sender and receiver use different keys |
| Ideal for encrypting large amounts of text | Generally used to encrypt short messages |
| The private key is shared between two parties | The public key can be used by anyone |
| The private key is kept secret | The public key is widely distributed |
| Generally used to protect disk drives and other data storage devices | Most often used to secure web sessions and emails |
Symmetric and asymmetric encryption
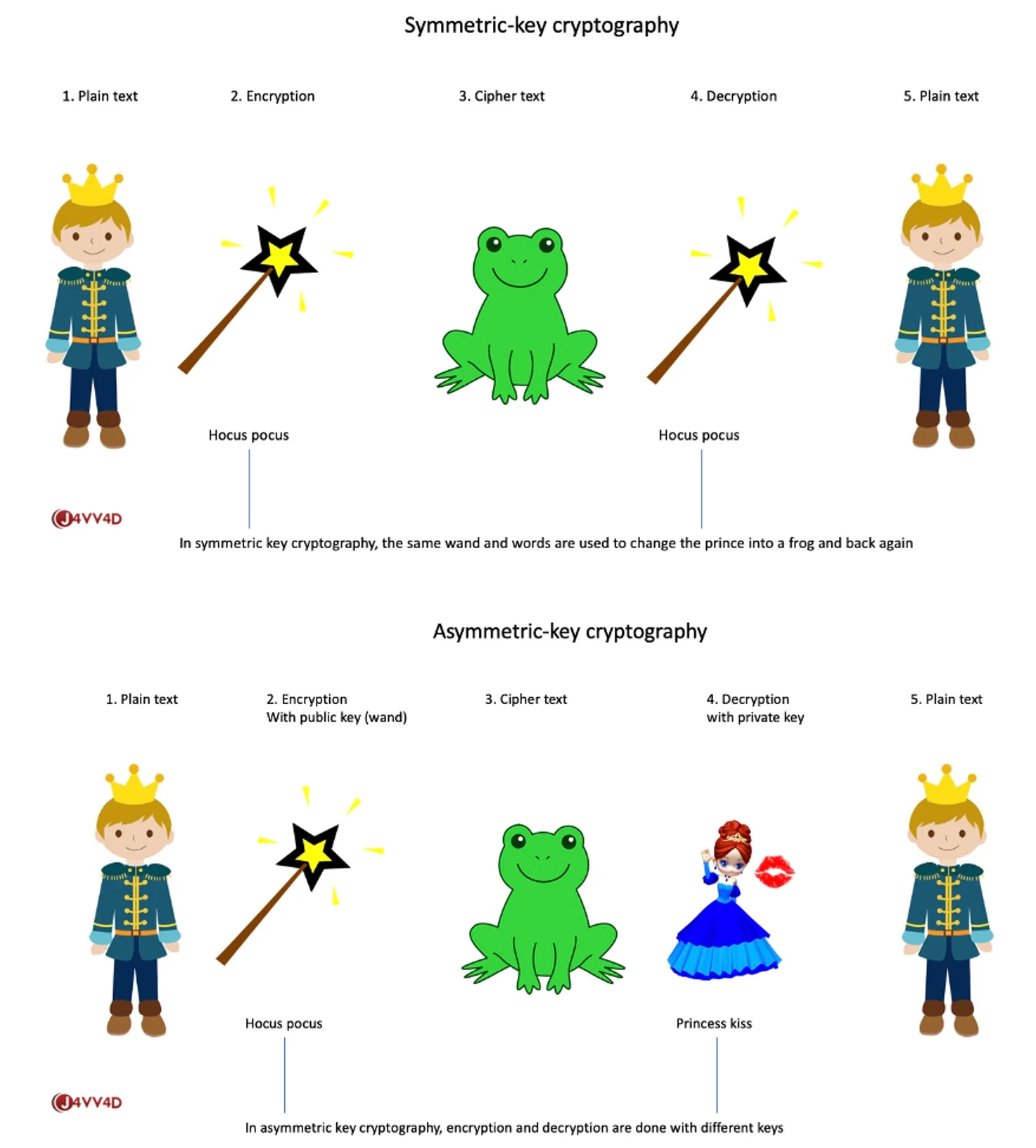
As mentioned in the chart above, there are two modes of encryption: symmetric encryption and asymmetric encryption, and keys are created using a symmetric or asymmetric algorithm depending on which method is being used. Before we examine the difference between public and private keys, it’s important to understand the differences between symmetric and asymmetric encryption.
Symmetric encryption involves only one key to encrypt and decrypt data. Both the sender and the recipient use the same key. Asymmetric or public key encryption requires a pair of keys, one public key and one private key, to encrypt and decrypt data. The public key can be openly distributed, allowing anyone to use the public key for encryption. However, the public key cannot be used to decrypt the ciphertext.
The illustrations below, courtesy of Javvad Malik, depict how symmetric and asymmetric encryption work.
Symmetric encryption is faster than asymmetric encryption because the algorithm used to encrypt data is less complex. But there is a major drawback to relying on a single key to encrypt and decrypt data. If that single key falls into the hands of a malicious actor, they can use it to decrypt the message and read its contents.
The primary drawback of asymmetric encryption is that the process requires significant computing power, which can slow down the process and make it unsuitable for long computing sessions.
Benefit of public keys
The greatest security benefit of using public key encryption is that a malicious actor cannot compromise machines and data without having the corresponding private key to decrypt them—no matter how widely distributed the public key may be.
And it helps that the algorithms used to encrypt these keys are hard to crack. The most commonly used algorithms for generating public keys are:
- Rivest–Shamir–Adleman (RSA)
- Elliptic curve cryptography (ECC)
- Digital signature algorithm (DSA)
Benefit of private keys
A private key is maintained as a secret key. The sender of a message can use the recipient’s public key—since it’s public, and anyone can view it—to encrypt the message. At this point, the message can be transmitted openly, but securely, over the internet, where then only the recipient can decrypt the message with the appropriate, corresponding private key. The security service provided when using a private key is simply confidentiality.
Public-private key pair
Asymmetric encryption involves a public key and a private key. The public key is used to encrypt data. The private key is used to decrypt data. The public—private key pair has a mathematical relationship, which means that the data encrypted with a public key can only be decrypted with the corresponding private key. Confidentiality, authentication and non-repudiation are security services that are provided when using the public key pair.
Public key infrastructure
Public key encryption is enabled by public key infrastructure (PKI), a broad framework that sets forth the technology and processes that secures internet connections and verifies the identity of users and machines. It’s used to secure communication over the internet using a public-private key pair, where only the intended recipient has the private, secret key. This public-private key pair relationship ensures that only the intended recipient can decrypt data that was encrypted using the public key.
Common applications of public keys
Using public key pairs not only ensures that the message is secure but it also provides confidence in the identity of the sender. A public key can encrypt data and it can also verify a digital signature. Public keys are used in connection with the following:
- Digital certificates
- Digital and machine identities
- Mass scale deployment of certificates
- Two-way SSL/TLS authentication
Digital certificates support identity verification and authentication. For example, when an individual signs a document digitally, their private key is used to digitally sign the document, and the recipient of the signed document verifies the authenticity of the signature with the sender’s public key. Email signing and code signing certificates have similar characteristics. For both certificates, the public key is used to verify the senders—or in the case of code signing certificates, the developer’s signature.
Conclusion
The primary difference between a private key and a public key is that the private key must remain a secret to the owner. Symmetric encryption, while much faster than asymmetric encryption, can be less secure due to the key distribution and management problems. Poorly distributed keys or mismanaged keys that fall into the hands of a bad actor may provide an opportunity to decrypt a message using the private key.
Either way, the strength of the encryption is directly related to the protection offered to the cryptographic keys. Venafi Control Plane for Machine Identities allows you to protect all the TLS keys and certificates, SSH keys, code signing keys and user certificates being used across your extended enterprise.
(This post has been updated. It was originally published on January 12, 2022.)
Related posts

2024 Machine Identity Management Summit
Help us forge a new era of cybersecurity
Looking to vulcanize your security with an identity-first strategy? Register today and save up to $100 with exclusive deals. But hurry, this sale won't last!
